Alert#
1EventID: 263
2Severity: High
3Event Time: Jun, 06, 2024, 03:12 PM
4Rule: SOC287 - Arbitrary File Read on Checkpoint Security Gateway [CVE-2024-24919]
5Level: Security Analyst
6Hostname: CP-Spark-Gateway-01
7Destination IP Address: 172.16.20.146
8Source IP Address: 203.160.68.12
9HTTP Request Method: POST
10Requested URL: 172.16.20.146/clients/MyCRL
11Request: aCSHELL/../../../../../../../../../../etc/passwd
12User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:126.0) Gecko/20100101 Firefox/126.0
13Alert Trigger Reason: Characteristics exploit pattern Detected on Request, indicative exploitation of the CVE-2024-24919.
14Device Action: AllowedCVE-2024-24919#
CVE-2024-24919 is a path traversal vulnerability in Check Point Security Gateway. It allows an unauthenticated attacker to read arbitrary files from the filesystem by sending a crafted POST request to the /clients/MyCRL endpoint with a path traversal sequence prefixed by aCSHELL/. The vulnerability was actively exploited in the wild shortly after disclosure, with attackers primarily targeting /etc/passwd and /etc/shadow to extract credentials for VPN accounts.
Identification#
Is the traffic coming from outside?#
The source IP 203.160.68.12 is an external address originating outside the corporate network. Traffic direction is Internet to Company Network. This was confirmed not to be a planned penetration test.
Is the source malicious?#
I checked 203.160.68.12 on AbuseIPDB - the IP belongs to China Unicom (Hong Kong) Operations Limited. It has been reported 2 times with 0% Confidence of Abuse.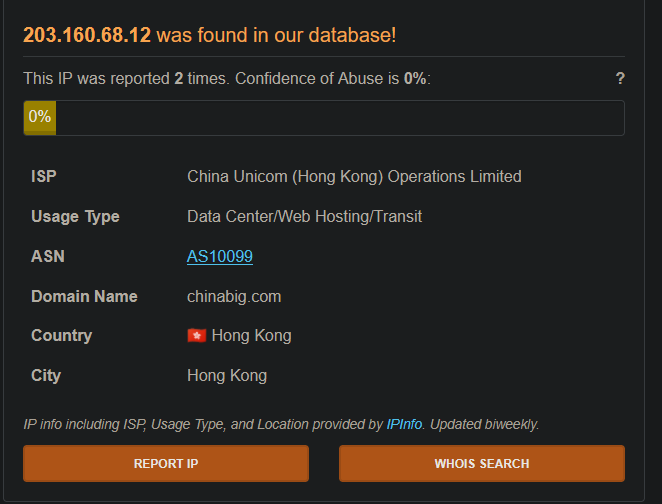
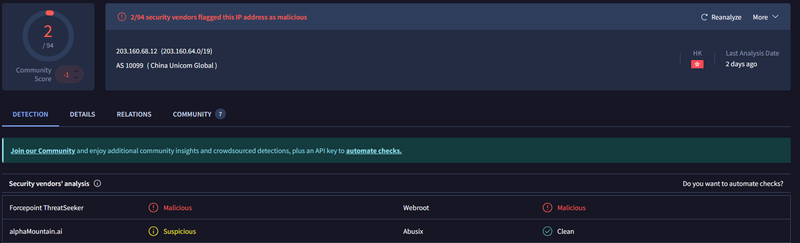
VirusTotal flagged the IP as malicious by 2/94 vendors - Forcepoint ThreatSeeker and Webroot both classify it as malicious, with alphaMountain.ai rating it suspicious.
What type of attack was attempted?#
The alert triggered on a POST request to /clients/MyCRL with the body aCSHELL/../../../../../../../../../../etc/passwd - a textbook CVE-2024-24919 exploitation attempt. The aCSHELL/ prefix is required by the vulnerable endpoint’s parsing logic, after which the path traversal sequence ../../../../../../../../../../ climbs to the filesystem root and reads /etc/passwd. This file contains the list of all system accounts and is the primary target for initial credential harvesting on Unix-based systems.
Did anyone else get targeted?#
Reviewing the firewall logs and access log, I identified a second attacker IP - 203.160.68.13 - in the same /19 subnet as the primary attacker. At 15:14:02 this IP submitted an identical exploit request targeting /etc/shadow, which stores hashed passwords. This request returned HTTP 403 and was blocked.

The coordinated use of two IPs from the same subnet within two minutes suggests a single threat actor using multiple egress points.
Did the attack succeed?#
Yes. The access log confirms the initial request from 203.160.68.12 at 15:12:45 returned HTTP 200 with a response size of 1256 bytes - larger than a typical error response, indicating the server returned the contents of /etc/passwd. The subsequent POST to / at 15:15:01 also returned HTTP 200, suggesting the attacker sent a follow-up request after the successful file read.
1203.160.68.12 "POST /clients/MyCRL HTTP/1.1" 200 1256 "aCSHELL/../../../../../../../../../../etc/passwd"
2203.160.68.13 "POST /clients/MyCRL HTTP/1.1" 403 314 "aCSHELL/../../../../../../../../../../etc/shadow"
3203.160.68.12 "POST / HTTP/1.1" 200 512Triage Decision#
What is the impact level?#
The attacker successfully read /etc/passwd from the Check Point Security Gateway 172.16.20.146, obtaining the full list of system and VPN accounts. A second attacker IP from the same subnet attempted to read /etc/shadow but was blocked. The gateway is a network security device - credential exposure at this level could enable VPN account compromise and lateral movement into the internal network. Escalated to Tier 2.
Containment#
Is the attacker still active?#
The last observed request from the attacker IPs was at 15:15:01. The OS log entry at 15:30 PM shows a local loopback event on 172.16.20.146 with no associated external traffic, so no active attacker connection was present at that time. Both IPs 203.160.68.12 and 203.160.68.13 were blocked at the perimeter firewall.
Is the vulnerable endpoint still exposed?#
The /clients/MyCRL endpoint on 172.16.20.146 remains vulnerable until the Check Point hotfix for CVE-2024-24919 is applied. The gateway was isolated from external access pending patching and the case was escalated to Tier 2 for credential rotation on all accounts present in the dumped /etc/passwd file.
IOCs#
IPs
- 203.160.68.12 - primary attacker IP
- 203.160.68.13 - secondary attacker IP
Endpoints
- 172.16.20.146` (CP-Spark-Gateway-01) - compromised Check Point Security Gateway
Requests
- aCSHELL/../../../../../../../../../../etc/passwd - successful file read payload
- aCSHELL/../../../../../../../../../../etc/shadow - blocked file read attempt