Alert#
1EventID : 120
2Event Time : Mar, 01, 2022, 10:10 AM
3Rule : SOC170 - Passwd Found in Requested URL - Possible LFI Attack
4Level : Security Analyst
5Hostname : WebServer1006
6Destination IP Address : 172.16.17.13
7Source IP Address : 106.55.45.162
8HTTP Request Method : GET
9Requested URL : https://172.16.17.13/?file=../../../../etc/passwd
10User-Agent : Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; .NET CLR 1.1.4322)
11Alert Trigger Reason : URL Contains passwd
12Device Action : AllowedIdentification#
Is the traffic coming from outside?#
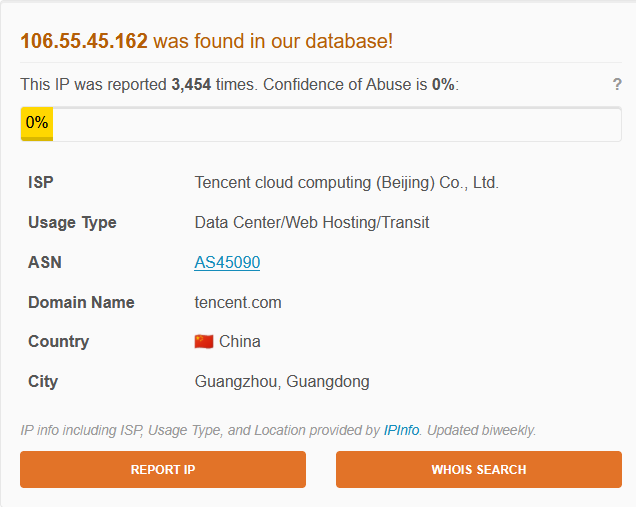
The source IP 106.55.45.162 is an external address belonging to Tencent Cloud Computing (Beijing) Co., Ltd. (AS45090, Guangzhou, Guangdong, China). The destination 172.16.17.13 is an internal address. Traffic direction is Internet to Company Network. This was confirmed not to be a planned test.
Is the source malicious?#
AbuseIPDB shows the IP has been reported 3,454 times with a Confidence of Abuse of 0%. The Data Center/Web Hosting usage type and Chinese cloud provider context are consistent with attacker-controlled VPS infrastructure.
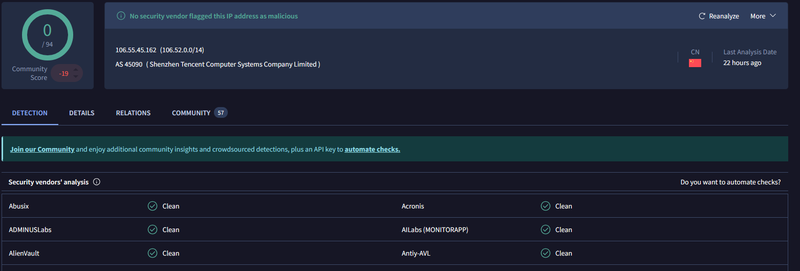
VirusTotal returned 0/94 detections, however the community score is -19 with 57 community comments - a strong negative signal indicating prior malicious activity reported by the community despite no vendor detections.
What type of attack was attempted?#
The alert triggered on a GET request to /?file=../../../../etc/passwd - a Local File Inclusion (LFI) attack using path traversal. The file parameter is used to specify a file to include server-side. By supplying ../../../../etc/passwd, the attacker attempts to traverse out of the web root and read the system’s account file, which contains usernames and can reveal service accounts and system configuration. The outdated User-Agent (MSIE 6.0 / Windows NT 5.1) is a fingerprint commonly seen in automated scanning tools.
Reviewing the raw log confirmed the request details:
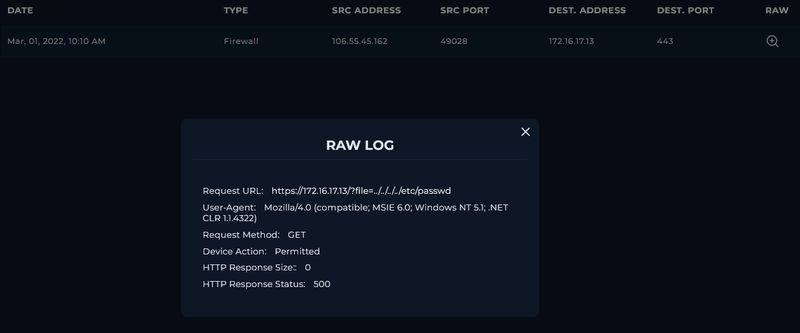
1Request URL: https://172.16.17.13/?file=../../../../etc/passwd
2Request Method: GET
3Device Action: Permitted
4HTTP Response Size: 0
5HTTP Response Status: 500Only one connection from 106.55.45.162 was observed in the firewall logs - a single probe rather than a multi-payload enumeration campaign.
Did anyone else get targeted?#
Log review shows only 172.16.17.13 (WebServer1006) was targeted. No other internal hosts were involved.
Did the attack succeed?#
No. The server returned HTTP 500 with a response size of 0 bytes. An HTTP 500 indicates an internal server error - the application failed to process the request but did not return the file contents. A successful LFI would return HTTP 200 with a non-zero response body containing the file data. The attack did not succeed.
Triage Decision#
True Positive. A single LFI probe from an external Tencent Cloud IP was correctly allowed through to the application layer and was rejected with HTTP 500. No Tier 2 escalation required.
What is the impact level?#
Low. The attack did not succeed and no data was returned. However, the HTTP 500 response indicates the application attempted to process the file parameter rather than rejecting it at input validation - the endpoint may be vulnerable to LFI with a different traversal depth or encoding.
Containment#
Is the attacker still active?#
Only one connection was logged at 10:10 AM on Mar 01, 2022. No follow-up requests were observed.
Is the vulnerable endpoint still exposed?#
The ?file= parameter on 172.16.17.13 remains exposed. The HTTP 500 response suggests the parameter reaches the filesystem layer, making it a candidate for further LFI testing with alternate traversal sequences or encoding bypasses. The endpoint should be reviewed by the application security team.
Actions taken#
106.55.45.162 was blocked at the firewall. The ?file= parameter on WebServer1006 was flagged for input validation review.
IOCs#
IPs
- 106.55.45.162 - attacker IP (Tencent Cloud AS45090, Guangzhou, CN)
URLs
- hxxps://172.16.17[.]13/?file=../../../../etc/passwd - LFI payload
User-Agent
- Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; .NET CLR 1.1.4322)