Alert#
1EventID: 115
2Severity: High
3Event Time: Feb, 25, 2022, 11:34 AM
4Rule: SOC165 - Possible SQL Injection Payload Detected
5Hostname: WebServer1001
6Destination IP Address: 172.16.17.18
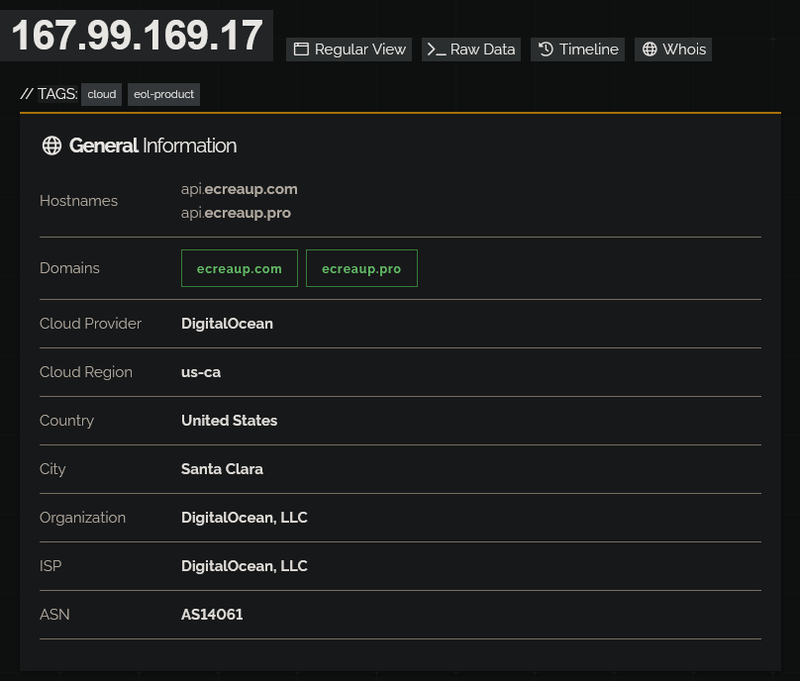
7Source IP Address: 167.99.169.17
8HTTP Request Method: GET
9Requested URL: https://172.16.17.18/search/?q=%22%20OR%201%20%3D%201%20--%20-
10User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1
11Alert Trigger Reason: Requested URL Contains OR 1 = 1
12Device Action: AllowedIdentification#
Is the traffic coming from outside?#
Is the source malicious?#
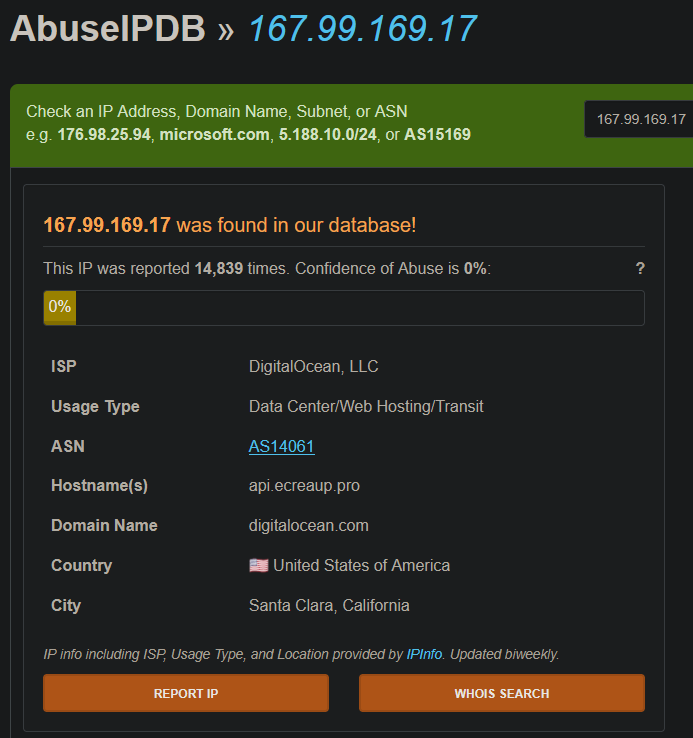
AbuseIPDB shows the IP has been reported 14,839 times, however the Confidence of Abuse score is 0%, which can occur when reports are old or unverified. Despite the low confidence score, the volume of historical reports and the DigitalOcean VPS hosting context are consistent with attacker infrastructure.
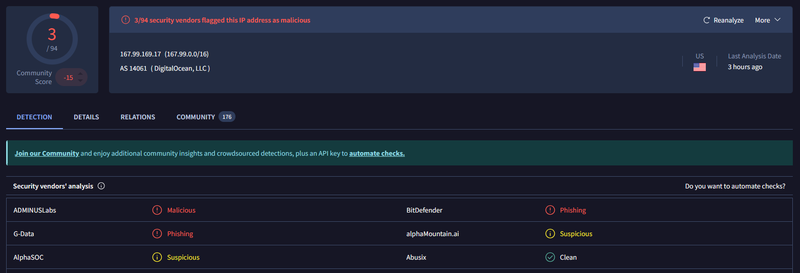
VirusTotal flagged the IP as malicious by 3/94 vendors. The low detection count combined with the AbuseIPDB history suggests this IP has been used for multiple abuse campaigns over time.
What type of attack was attempted?#
Reviewing the firewall logs, I observed multiple inbound connections from 167.99.169.17 to 172.16.17.18 on port 443 between 11:30 AM and 11:34 AM, all logged as permitted.

Examining the full request log, the attacker targeted the /search/ endpoint with a series of classic SQL injection payloads delivered via the q GET parameter:
1https://172.16.17.18/search/?q=' OR '1
2https://172.16.17.18/search/?q='
3https://172.16.17.18/search/?q=' OR 'x'='x
4https://172.16.17.18/search/?q=1' ORDER BY 3--+
5https://172.16.17.18/search/?q=" OR 1 = 1 -- -Did anyone else get targeted?#
Log review shows all requests from 167.99.169.17 targeted exclusively 172.16.17.18 on the /search/ endpoint on WebServer1001. No other internal hosts were targeted during this timeframe.
Did the attack succeed?#
No. Every SQL injection request returned HTTP 500 Internal Server Error with a response size of 948 bytes, consistent with a generic error page. No successful data extraction or authentication bypass was observed.
Triage Decision#
What is the impact level?#
The attacker probed the /search/ endpoint with multiple SQL injection payloads. All requests returned HTTP 500 - the application crashed on the input but did not expose data. The attack was malicious and intentional but did not succeed. No escalation to L2 is required. Containment actions and WAF rule updates are sufficient.
Containment#
Is the attacker still active?#
The last observed request from 167.99.169.17 was at 11:34 AM. No further connections were observed after that timestamp in the firewall logs.
Is the vulnerable endpoint still exposed?#
The /search/ endpoint on 172.16.17.18 remains exposed and appears to pass unsanitized input to the backend, as evidenced by the HTTP 500 responses to SQLi payloads. Input validation and parameterized queries should be reviewed immediately.
Is the web server still compromised?#
No compromise was achieved. The server returned errors on all injection attempts and no successful response (HTTP 200 with data) was observed. Source IP 167.99.169.17 was blocked at the firewall.
IOCs#
| Type | Value | Source | Blocked |
|---|---|---|---|
| IP | 167.99.169[.]17 | Firewall / WAF logs | Yes |
| URL | hxxps://172.16.17[.]18/search/?q=%22%20OR%201%20%3D%201%20--%20- | WAF alert | Yes |
| Domain | ecreaup[.]com | Shodan / AbuseIPDB | Yes |
| Domain | ecreaup[.]pro | Shodan / AbuseIPDB | Yes |