Alert#
1EventID : 118
2Event Time : Feb, 28, 2022, 04:12 AM
3Rule : SOC168 - Whoami Command Detected in Request Body
4Level : Security Analyst
5Hostname : WebServer1004
6Destination IP Address : 172.16.17.16
7Source IP Address : 61.177.172.87
8HTTP Request Method : POST
9Requested URL : https://172.16.17.16/video/
10User-Agent : Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1)
11Alert Trigger Reason : Request Body Contains whoami string
12Device Action : AllowedIdentification#
Is the traffic coming from outside?#
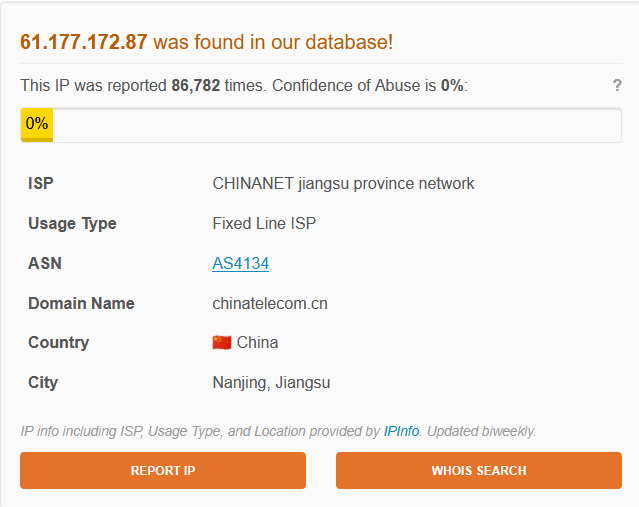
The source IP 61.177.172.87 falls outside any RFC 1918 private range and resolves to CHINANET Jiangsu Province Network (AS4134, Nanjing, China). Traffic direction is Internet to Company Network. This was confirmed not to be a planned penetration test.
Is the source malicious?#
I checked 61.177.172.87 on AbuseIPDB - the IP has been reported 86,782 times with a Confidence of Abuse of 0%, indicating high historical noise but no active campaign score.
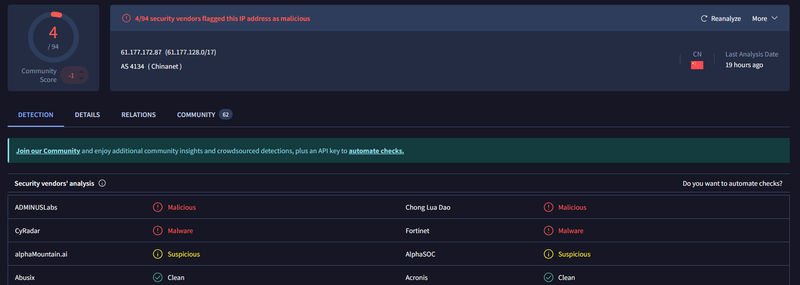
VirusTotal flagged the IP as malicious by 4/94 vendors. Community score is -1.
What type of attack was attempted?#
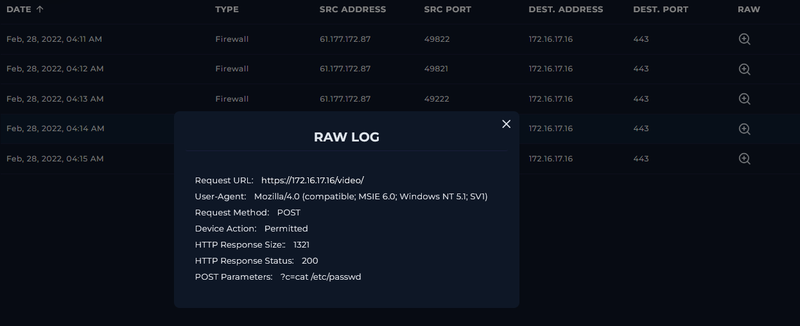
The attacker exploited a command injection vulnerability on the /video/ endpoint by passing OS commands through the ?c= POST parameter. Command injection occurs when user-supplied input is passed unsanitized to a system shell, allowing arbitrary command execution in the context of the web server process. The attacker ran five commands in sequence - ls, whoami, uname, cat /etc/passwd, and cat /etc/shadow. The use of a spoofed legacy User-Agent (MSIE 6.0 / Windows NT 5.1) indicates deliberate evasion.
Did anyone else get targeted?#
Reviewing the firewall logs, all five requests were directed exclusively at 172.16.17.16:443. No other destination addresses appeared in the log window and no lateral movement was observed.

Did the attack succeed?#
Yes. All five POST requests returned HTTP 200 with varying response sizes ranging from 910 to 1501 bytes, consistent with the server executing each command and returning its output.
Triage Decision#
What is the impact level?#
The attacker achieved confirmed remote code execution on 172.16.17.16 (WebServer1004), successfully reading both /etc/passwd and /etc/shadow. Combined with the whoami and uname output, the attacker obtained a full OS fingerprint and the privilege context of the web process. Escalated to Tier 2.
Containment#
Is the attacker still active?#
The last observed request from 61.177.172.87 was at 04:15 AM on Feb 28, 2022. No further entries appeared in the log window beyond that timestamp. The IP was blocked at the perimeter firewall to prevent any follow-up connection attempts.
Is the vulnerable endpoint still exposed?#
The /video/ endpoint on 172.16.17.16 was passing the ?c= parameter directly to the system shell with no sanitization or allowlist enforcement. The endpoint was taken offline pending a code-level fix. Input validation restricting the ?c= parameter to expected values was flagged as mandatory before redeployment.
Actions taken#
61.177.172.87 was blocked at the perimeter firewall. 172.16.17.16 was isolated from external access and escalated to Tier 2 for credential rotation on all accounts present in the dumped /etc/passwd and /etc/shadow files.
IOCs#
IPs
- 61.177.172.87 - attacker IP
Hosts
- 172.16.17.16 (WebServer1004) - compromised web server
Requests
- ?c=ls
- ?c=whoami
- ?c=uname
- ?c=cat /etc/passwd
- ?c=cat /etc/shadow
User-Agents
- Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1) - spoofed legacy User-Agent used across all requests