Objective#
Replay a PCAP file through Suricata integrated with Wazuh to practice network-based threat detection, analyze generated alerts, reconstruct the infection chain, and map findings to MITRE ATT&CK.
PCAP Overview#
The PCAP file contains network traffic captured from an infected Windows 7 (64-bit) host on an internal network.
Timeline:
- Start: Feb 8, 2021 @ 17:59:18
- End: Feb 8, 2021 @ 18:18:18
- Duration: ~19 minutes
Hosts involved:
| Host | Type | Role |
|---|---|---|
| 10.2.8.101 | Internal | Infected Windows 7 victim |
| 10.2.8.2 | Internal | Gateway / DNS — target of lateral movement |
| 8.208.10.147 | External | roanokemortgages.com — payload delivery |
| 213.5.229.12 | External | satursed.com — Hancitor C2 |
| 198.211.10.238 | External | Cobalt Strike / Meterpreter / Dridex C2 |
| 185.100.65.29 | External | Ficker Stealer C2 |
| 162.241.149.195 | External | Phishing / Let’s Encrypt IDN |
| 54.235.147.252 | External | api.ipify.org — IP lookup |
Victim OS: Windows 7 64-bit, identified via User-Agent strings:
- Windows NT 6.1; Win64; x64; Trident/7.0 (Internet Explorer 11)
- Windows NT 6.1; WOW64; Trident/5.0 (Internet Explorer 9)
What Suricata Detected#
Suricata generated 423 alerts forwarded to Wazuh via eve.json.
All alerts appeared under Wazuh rule.id: 86601 in the Security Events dashboard.

Suricata Signature IDs triggered:
| Signature ID | Rule Name | Category |
|---|---|---|
| 2034127 | ET MALWARE Tordal/Hancitor/Chanitor Checkin | Malware C2 |
| 2033713 | ET MALWARE Cobalt Strike Beacon Observed | Malware C2 |
| 2028765 | ET JA3 Hash - [Abuse.ch] Possible Dridex | Malware C2 |
| 2035651 | ET MALWARE Meterpreter or Other Reverse Shell SSL Cert | Malware C2 |
| 2031074 | ET MALWARE Win32/Ficker Stealer Activity | Malware |
| 2014819 | ET INFO Packed Executable Download | Execution |
| 2018358 | ET HUNTING GENERIC SUSPICIOUS POST to Dotted Quad | Hunting |
| 2024227 | ET PHISHING Lets Encrypt Free SSL Cert with IDN/Punycode | Phishing |
| 2047702 | ET INFO External IP Lookup Domain (ipify.org) in DNS | Reconnaissance |
| 2029622 | ET INFO External IP Lookup (ipify.org) | Reconnaissance |
| 2067085 | ET INFO NTLM Session Setup Request - Negotiate | Lateral Movement |
Infection Chain Reconstruction#
By correlating alert timestamps, a complete infection chain is visible:
Payload Delivery
1ET INFO Packed Executable Download
2→ src: 10.2.8.101 → dest: 8.208.10.147 (roanokemortgages.com)
3→ File: /6lhjgfdghj.exe (42,405 bytes — application/octet-stream)
4→ Hancitor dropper delivered over HTTP
5→ MITRE T1105: Ingress Tool Transfer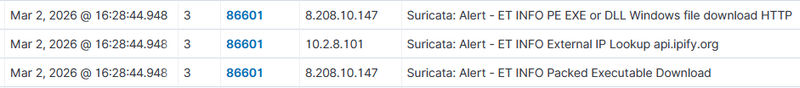
1"http": {
2 "hostname": "roanokemortgages.com",
3 "protocol": "HTTP/1.1",
4 "http_method": "GET",
5 "http_content_type": "application/octet-stream",
6 "length": "42405",
7 "url": "/6lhjgfdghj.exe",
8 "http_user_agent": "Mozilla/5.0 (Windows NT 6.1; Win64; x64; Trident/7.0; rv:11.0) like Gecko",
9 "status": "200"
10 },
11 "files": [
12 {
13 "filename": "/6lhjgfdghj.exe",
14 "size": 42405,
15 "stored": false,
16 "state": "UNKNOWN",
17 "tx_id": 2,
18 "gaps": false
19 }Reconnaissance
1ET INFO External IP Lookup Domain (ipify.org) in DNS Lookup
2ET INFO External IP Lookup (ipify.org)
3→ src: 10.2.8.101 → dest: 54.235.147.252 (api.ipify.org)
4→ Malware checks victim's external IP — standard post-infection behavior
5→ MITRE T1590: Gather Victim Network InformationHancitor C2 Check-in
1ET MALWARE Tordal/Hancitor/Chanitor Checkin
2ET HUNTING GENERIC SUSPICIOUS POST to Dotted Quad
3→ src: 10.2.8.101 → dest: 213.5.229.12 (satursed.com)
4→ Hancitor dropper reports to C2, receives next-stage payload instructions
5→ MITRE T1071.001: Application Layer Protocol: Web ProtocolsSecondary Payload C2
1ET MALWARE Cobalt Strike Beacon Observed
2ET MALWARE Meterpreter or Other Reverse Shell SSL Cert
3ET HUNTING Suspicious Empty SSL Certificate — Cobalt Strike
4ET JA3 Hash - [Abuse.ch] Possible Dridex
5→ src: 10.2.8.101 → dest: 198.211.10.238
6→ Cobalt Strike beacon and Dridex banking trojan establish C2 over TLS
7→ MITRE T1071.001, T1573.001: Encrypted ChannelInfostealer Activity
1ET MALWARE Win32/Ficker Stealer Activity
2→ src: 10.2.8.101 → dest: 185.100.65.29
3→ Ficker Stealer active — targets browsers, credentials, crypto wallets
4→ MITRE T1041: Exfiltration Over C2 ChannelLateral Movement
1ET INFO NTLM Session Setup Request - Negotiate
2→ src: 10.2.8.101 → dest: 10.2.8.2 (internal gateway)
3→ NTLM authentication attempt against internal host via SMB
4→ MITRE T1550.002: Pass the Hash / T1021.002: SMBPhishing Infrastructure
1ET PHISHING Lets Encrypt Free SSL Cert with IDN/Punycode Domain
2→ dest: 162.241.149.195
3→ Contact with phishing domain using lookalike certificate
4→ MITRE T1566: PhishingDetection Gap#
All 423 Suricata alerts arrived in Wazuh at rule.level 3 — informational severity. This is a default integration gap: Wazuh rule 86601 maps all Suricata alerts to level 3 regardless of the underlying Suricata severity.
Response#
To escalate Cobalt Strike detections to critical severity, a custom rule
was added to /var/ossec/etc/rules/local_rules.xml:
1<group name="suricata,">
2 <rule id="100002" level="12">
3 <if_sid>86601</if_sid>
4 <field name="data.alert.signature">Cobalt Strike</field>
5 <description>Suricata: Cobalt Strike C2 Beacon — Critical</description>
6 <mitre>
7 <id>T1071.001</id>
8 </mitre>
9 </rule>
10</group>The recommended response would be:
- Block all identified external C2 IPs at the perimeter firewall
- Isolate the infected host (10.2.8.101) from the network immediately
- Search for the dropper binary (6lhjgfdghj.exe) across all endpoints
- Reset credentials for all accounts active on the infected host
- Hunt for Cobalt Strike beacon artifacts in memory and persistence mechanisms
Conclusion#
Replaying a PCAP through Suricata integrated with Wazuh produced 423 alerts covering a complete infection chain — from initial payload delivery through C2 communication, credential theft, and lateral movement attempts.
Key takeaways:
- Hancitor acted as initial dropper, deploying Cobalt Strike, Dridex, and Ficker Stealer
- Suricata + Wazuh provides full visibility into multi-stage malware behavior
- Default Wazuh integration sets all Suricata alerts at level 3 — custom rules required for critical escalation
- Correlating timestamps across 11 signature IDs revealed a complete 7-stage infection chain