Description:
The Client is in full control. Bypass the authentication and read the key to get the Flag.
initial analysis#
1$ file Bypass.exe
2Bypass.exe: PE32 executable for MS Windows 4.00 (console), Intel i386 Mono/.Net assembly, 3 sections1C:\Users\f\Desktop>Bypass.exe
2Enter a username: hi
3Enter a password: hi
4Wrong username and/or password
5Enter a username: aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
6Enter a password: aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
7Wrong username and/or password
8Enter a username:reversing with dnspy#
Код отримує доступ до вбудованого ресурсу з іменем "0". ці дані передаються у метод 3 класу 7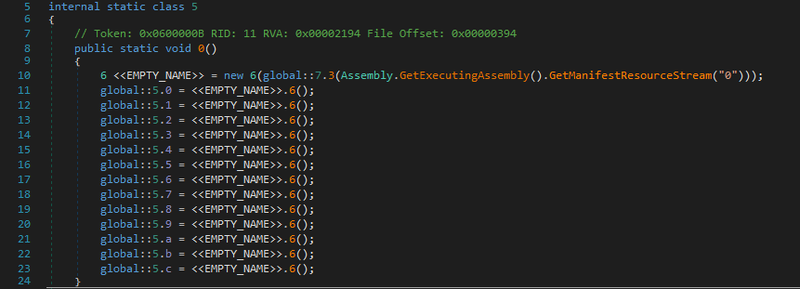
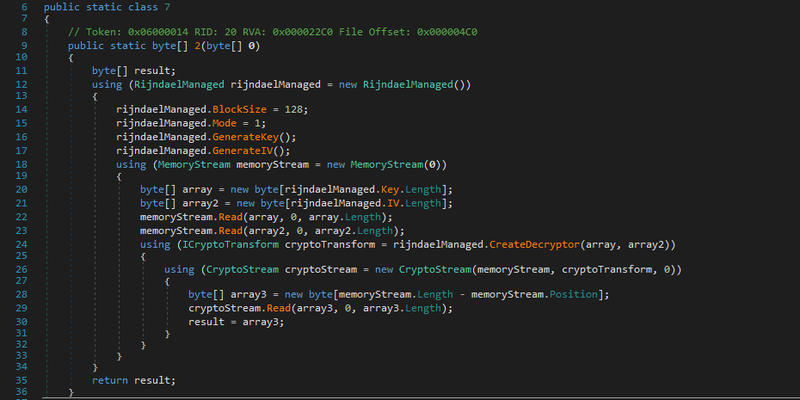
1byte[] array = new byte[rijndaelManaged.Key.Length];
2byte[] array2 = new byte[rijndaelManaged.IV.Length];
3memoryStream.Read(array, 0, array.Length);
4memoryStream.Read(array2, 0, array2.Length);solution#
1from Crypto.Cipher import AES
2from Crypto.Util.Padding import unpad
3
4with open("0.bin", "rb") as f:
5 d = f.read()
6
7k_s = 32
8iv_s = 16
9
10key = d[:k_s]
11iv = d[k_s:k_s + iv_s]
12enc_d= d[k_s + iv_s:]
13
14c = AES.new(key, AES.MODE_CBC, iv)
15dec_d = c.decrypt(enc_d)
16
17with open("re.bin", 'wb') as f:
18 f.write(dec_d)
19
20print("re.bin\ndone")1$ python3 dec.py
2re.bin
3done
4
5$ cat re.bin
6<Wrong username and/or password$Enter a username: $Enter a password: |ThisIsAReallyReallySecureKeyButYouCanReadItFromSourceSoItSucks:Please Enter the secret Key: 4Nice here is the Flag:HTB{}Wrong Key▒SuP3rC00lFL4g�This executable has been obfuscated by using RustemSoft Skater .NET Obfuscator Demo version. Please visit RustemSoft.com for more information.�This executable has been obfuscated by using RustemSoft Skater .NET Obfuscator Demo version. Please visit RustemSoft.com for more information.�This executable has been obfuscated by using RustemSoft Skater .NET Obfuscator Demo version. Please visit RustemSoft.com for more information.�This executable has been obfuscated by using RustemSoft Skater .NET Obfuscator Demo version. Please visit RustemSoft.com for more information. we see HTB{}Wrong Key▒SuP3rC00lFL4g so flag is HTB{SuP3rC00lFL4g}