TL;DR#
A Go-based backdoor that copies itself to C:\Systemlogs\logscheck.exe,
establishes persistence via HKCU\...\Run\HealthCheck, enumerates
connected drives via GetDriveType, and attempts to connect to
malware.invalid.com.
Initial Analysis#
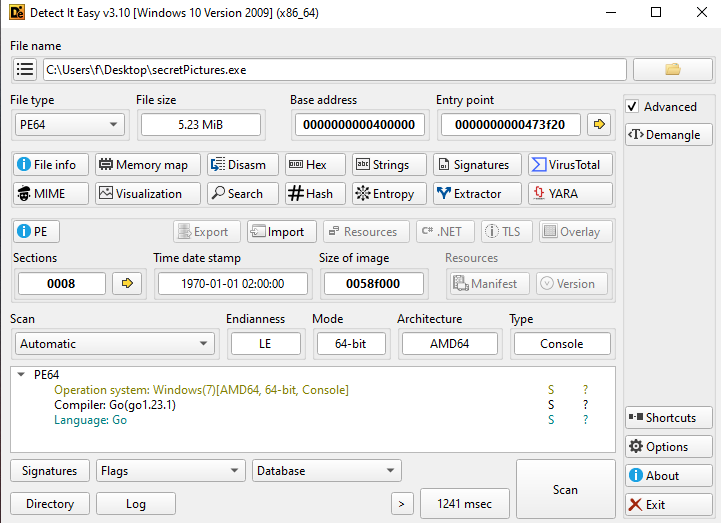
1secretPictures.exe: PE32+ executable (console) x86-64, 8 sections
2SHA256: 80e82415a26ac7c0124bbaa2133192dadd51cbc5ed22b202ebb24f6fddf8c8abStatic analysis confirmed the binary was written in Go.
Sandbox Analysis#
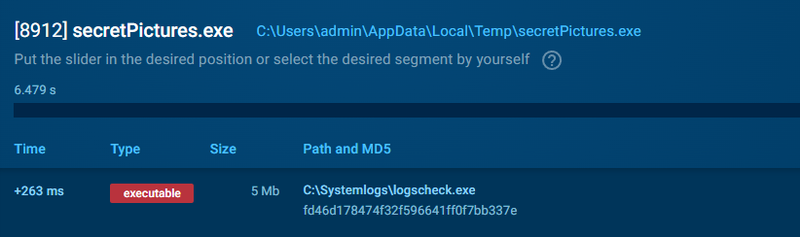
Seconds after execution the sample copied itself to C:\Systemlogs\
and renamed itself to logscheck.exe.
Persistence#
A registry Run key was set to execute logscheck.exe on every user login:
1HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\HealthCheck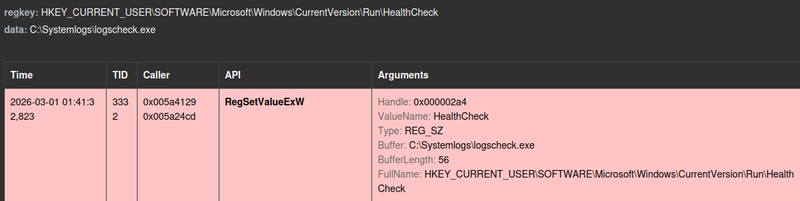
C2 Communication#
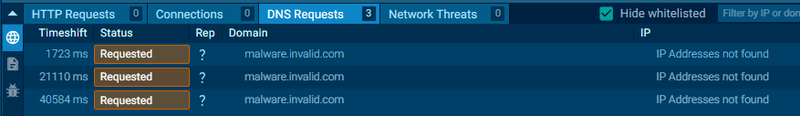
The sample attempted to connect to the hardcoded domain malware.invalid.com.
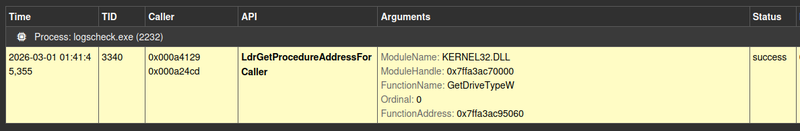
Drive Enumeration#
The sample called the GetDriveType WinAPI function to enumerate all
connected drives — likely to identify removable media or network shares
for lateral movement or data staging.
IOCs#
Files
- secretPictures.exe
- SHA256: 80e82415a26ac7c0124bbaa2133192dadd51cbc5ed22b202ebb24f6fddf8c8ab
- C:\Systemlogs\logscheck.exe — persistence copy
Registry
- HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\HealthCheck
Network
- C2 Domain: malware.invalid.com