TL;DR#
A victim clicked a phishing link impersonating a corporate login page, leading to credential theft. The attacker used stolen credentials to gain RDP access, then escalated privileges via SeManageVolumeExploit, deployed malicious DLLs using certutil, and established persistence through a hidden VBS script in the Startup folder.
Initial Access#
Phishing URL#
By analyzing the victim’s Chrome history using ChromeHistoryView, I identified that on 2025-05-23 14:20:07 the victim visited the legitimate company intranet. Two days later, on 2025-05-25 13:36:42, they clicked a phishing URL that harvested their credentials:
1http://intranet.wowzainc.co.th/landing.php 2025-05-23 14:20:07
2https://login.wowzalnc.co.th/logon.php 2025-05-25 13:36:42 <- phishing
3https://mail.wowzainc.co.th/inbox.php 2025-05-23 14:21:17The phishing domain wowzalnc.co.th impersonates the legitimate wowzainc.co.th by replacing the letter i with l.
RDP Access#
Using the harvested credentials, the attacker gained remote access via RDP on 2025-05-27 11:59:57. This was confirmed by Event ID 4624 in Security.evtx with Logon Type 10 (RemoteInteractive):
1# Security.evtx / Event ID 4624
2Logon Type: 10
3Account Name: otello.j
4Account Domain: WORKSTATION6
5Logon ID: 0x2A017F
6Security ID: S-1-5-21-888844466-1397619329-4015378808-1001Privilege Escalation#
SeManageVolumeExploit#
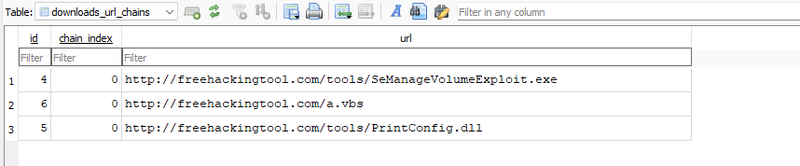
On 2025-05-28 12:36:59, the attacker visited freehackingtool.com and browsed its tools section:
1http://freehackingtool.com/ 2025-05-28 12:36:59
2http://freehackingtool.com/tools/ 2025-05-28 12:37:09
3http://freehackingtool.com/tools/ 2025-05-28 12:53:36
4http://freehackingtool.com/ 2025-05-28 12:55:02From this site, download attempts were made for three files: SeManageVolumeExploit.exe, a.vbs, and PrintConfig.dll.
At 2025-05-28 12:43:33, SeManageVolumeExploit.exe was successfully downloaded. This tool exploits the SeManageVolumePrivilege — a Windows privilege that allows volume-level operations such as mounting, dismounting, and defragmenting volumes. When abused, it can grant an attacker full control over the C: drive, enabling them to bypass access controls, manipulate the file system, and potentially execute arbitrary code.
Malware Deployment#
PrintConfig.dll — Malicious DLL via certutil#
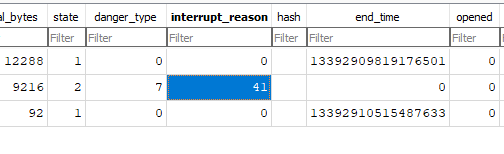
At 2025-05-28 12:44:01, the browser download of PrintConfig.dll was interrupted with interrupt code 41 (USER_SHUTDOWN — the browser was closed before the download completed).
To work around this, the attacker used the LOLBIN certutil.exe to download the file at 2025-05-28 12:45:37. This was confirmed by analyzing the CryptnetUrlCache/Metadata artifacts. The legitimate DLL at C:\Windows\system32\spool\drivers\x64\12\PrintConfig.dll was then removed and replaced with the malicious version.
At 2025-05-28 15:19:35, Windows Defender detected and flagged the replaced DLL:
1Name: Trojan:Win64/Meterpreter.E
2ID: 2147721833
3Severity: Severe
4Path: C:\Windows\system32\spool\drivers\x64\3\PrintConfig.dll
5 service: PrintNotify
6Detection Origin: Local machine
7User: NT AUTHORITY\SYSTEM
8Engine Version: AM: 1.1.25050.2tzres.dll — Secondary Malicious DLL#
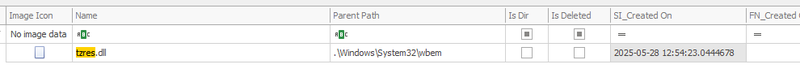
At 2025-05-28 12:54:23, a second malicious DLL tzres.dll was downloaded via certutil.exe and placed at C:\Windows\system32\wbem\tzres.dll.
PrintConfig.dll Execution#
From the PowerShell console history, I found that the attacker triggered execution of the malicious PrintConfig.dll by instantiating a COM object associated with the Windows spooler service:
1dir
2$type = [Type]::GetTypeFromCLSID("{854A20FB-2D44-457D-992F-EF13785D2B51}")
3$object = [Activator]::CreateInstance($type)
4dir
5reg add "HKCU\control panel\desktop" /v wallpaper /t REG_SZ /d "C:/Users/Public/Pictures/gg.bmp" /fThe CLSID {854A20FB-2D44-457D-992F-EF13785D2B51} is associated with the PrintNotify service. Instantiating it caused spoolsv.exe to load and execute the malicious PrintConfig.dll. Additionally, the attacker downloaded an image gg.bmp and set it as the desktop wallpaper — likely to signal successful compromise.
Persistence#
a.vbs — Startup Script#
At 2025-05-28 12:55:05, a.vbs was downloaded and moved to the Windows Startup folder to ensure execution on every boot:
1C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\a.vbsThe script creates a WScript.Shell object and silently runs systeminfo:
Set WshShell = CreateObject("WScript.Shell")
WshShell.Run "cmd.exe /c systeminfo", 0, Falsesysteminfo collects data via WMI, which triggers the WMI Provider Host (wmiprvse.exe). Since wmiprvse.exe executes all providers from the \wbem\ directory, this causes the malicious tzres.dll to be loaded automatically.
At 2025-05-28 12:56:11, the Hidden attribute was set on a.vbs to conceal it from the victim:
1a.vbs 12:56:11 BasicInfoChange Hidden|ArchiveAttack Timeline#
12025-05-23 14:20:07 - Victim visits legitimate intranet site
22025-05-25 13:36:42 - Victim clicks phishing URL, credentials harvested
32025-05-27 11:59:57 - Attacker gains RDP access as otello.j (Logon Type 10)
42025-05-28 12:36:59 - Attacker visits freehackingtool.com
52025-05-28 12:43:33 - SeManageVolumeExploit.exe successfully downloaded
62025-05-28 12:44:01 - Browser download of PrintConfig.dll interrupted (code 41)
72025-05-28 12:45:37 - PrintConfig.dll downloaded via certutil, replaces legitimate DLL
82025-05-28 12:54:23 - tzres.dll downloaded via certutil, placed in wbem\
92025-05-28 12:55:05 - a.vbs downloaded and placed in Startup folder
102025-05-28 12:56:11 - Hidden attribute set on a.vbs
112025-05-28 15:19:35 - Windows Defender detects PrintConfig.dll as Trojan:Win64/Meterpreter.EIOCs#
Domains
- login.wowzalnc.co.th — phishing domain (typosquat of wowzainc.co.th)
- freehackingtool.com — malware hosting
Files
- C:\Windows\system32\spool\drivers\x64\3\PrintConfig.dll — Trojan:Win64/Meterpreter.E
- C:\Windows\system32\wbem\tzres.dll — malicious secondary DLL
- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\a.vbs — persistence script
- SeManageVolumeExploit.exe — privilege escalation tool
Registry
- HKCU\control panel\desktop\wallpaper — set to C:/Users/Public/Pictures/gg.bmp
Accounts
- otello.j — compromised via phishing
Recommendations#
Immediate Actions
- Isolate the compromised workstation from the network
- Block domains
wowzalnc.co.thandfreehackingtool.comat the perimeter - Remove
a.vbsfrom the Startup folder - Restore legitimate
PrintConfig.dllandtzres.dllfrom a clean source - Reset credentials for
otello.jand audit for lateral movement - Review all RDP logon events (Event ID 4624, Logon Type 10) across the environment
Preventive Measures
- Enable MFA on all remote access solutions to mitigate phishing-based credential theft
- Restrict
certutil.exeusage via AppLocker or WDAC to prevent LOLBIN abuse - Enable and monitor Windows Defender alerts centrally via SIEM
- Audit and restrict
SeManageVolumePrivilegeassignments - Deploy DNS filtering to block known phishing and malware-hosting domains